
Introduction
The NIS2 Directive (EU 2022/2555) has now been transposed into national law across EU Member States, fundamentally changing the cybersecurity landscape for energy infrastructure. For investors in Battery Energy Storage Systems (BESS), this represents a paradigm shift – cybersecurity is no longer an optional add-on but a mandatory component of every investment.
Critically, even if your energy storage facility doesn’t directly meet the criteria for “essential” or “important” entities, NIS2 requirements will still affect you. Why? Because your energy offtakers – aggregators, large utilities, grid operators – are NIS2 entities and will require their suppliers (including BESS operators) to meet supply chain security standards.
This article provides a practical guide: what specific actions to take, which certifications and security policies to require from suppliers, what tests to conduct before commissioning, and how to verify compliance.
Why Does NIS2 Apply to Every Grid-Connected Energy Storage System?
Direct Regulatory Coverage
The energy sector is explicitly listed in Annex I of the NIS2 Directive (https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32022L2555) as a sector of high criticality. Point 1 of this annex covers undertakings engaged in generation, transmission, distribution, storage, and supply of energy. Energy storage operators fall directly within this definition.
If your company meets the medium-sized enterprise criteria (more than 50 employees or over EUR 10 million turnover), you are a NIS2 entity.
Indirect Coverage Through Supply Chain – The Key Mechanism
Even if your energy storage system is small and you don’t meet the criteria for direct coverage, NIS2 requirements will still reach you. Article 21(2)(d) of NIS2 explicitly requires essential and important entities to manage “supply chain security, including security-related aspects concerning the relationships between each entity and its direct suppliers or service providers.”
As law firm DLA Piper explains in their analysis of NIS2 supply chain requirements (https://www.dlapiper.com/en-us/insights/publications/2025/12/nis2-directive-explained-part-3-supply-chain-security), entities covered by the directive must manage cybersecurity risk throughout their supply chain, including subcontractors. The NIS2 Implementing Regulation indicates that contractual clauses should include cybersecurity requirements for subcontractors of direct suppliers as well.
In practice, this means:
- The aggregator purchasing energy from your storage facility is a NIS2 entity
- The Distribution System Operator (DSO) you’re connected to is a NIS2 entity
- The large corporate offtaker with whom you have a PPA may be a NIS2 entity
Each of these entities will contractually require you to meet security standards. Even if your company isn’t directly regulated, regulated customers will “flow down” NIS2 requirements to their suppliers contractually – this is the mechanism of so-called “flow-down clauses.”
Practical Conclusion: Every grid-connected energy storage system will sooner or later encounter NIS2 requirements – either as a directly regulated entity or as part of a regulated entity’s supply chain.
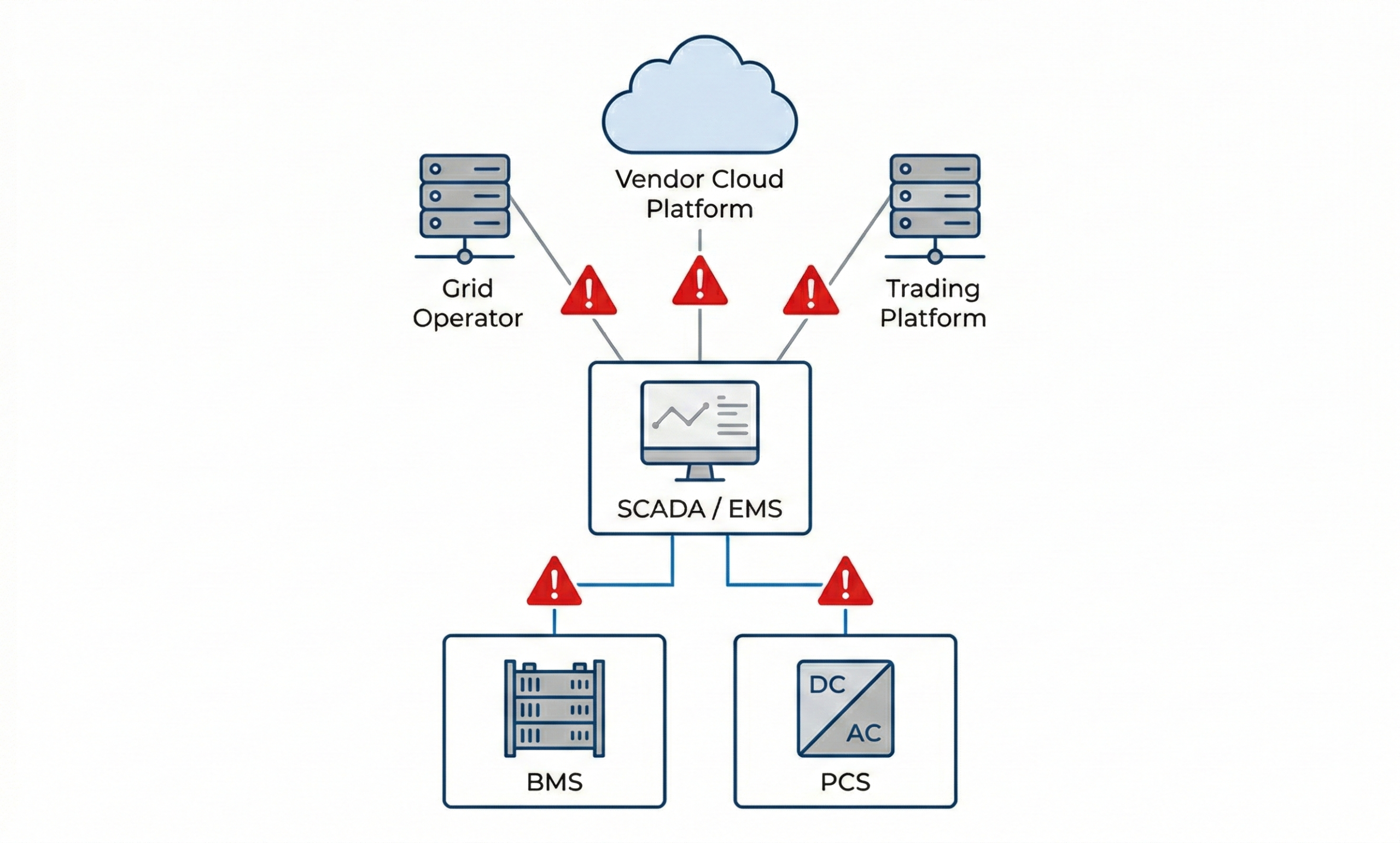
BESS Architecture from a Cybersecurity Perspective
A BESS is not just containers with batteries – it’s a complex information system with multiple potential attack points. Understanding the architecture is crucial for proper risk assessment.
BESS System Layers:
Layer 1: Control Systems (OT)
At the lowest level are systems directly controlling the storage facility: the Battery Management System (BMS) monitoring cell status, temperatures, and voltages, and the Power Conversion System (PCS) responsible for energy conversion between DC and AC. These components communicate using industrial protocols such as Modbus, CAN bus, or IEC 61850. Compromise of this layer can lead to physical battery damage or grid instability.
Layer 2: Supervision and Management
Above this is the SCADA/EMS (Energy Management System) layer – the “brain” of the installation. This system collects data from BMS and PCS, executes optimization strategies, and communicates with grid operators and aggregators. SCADA/EMS is typically an industrial server with a web interface, often remotely accessible. This is the most common attack target – gaining control of the EMS gives an attacker full power over the storage facility.
Layer 3: External Connectivity
An energy storage system doesn’t operate in isolation. It communicates with multiple external systems: the BESS manufacturer’s cloud platform (monitoring, diagnostics, updates), the optimizer/aggregator system (control signals, market prices), the distribution grid operator (power curtailment commands, FCR signals), and remote service access for O&M. Each of these connections is a potential attack vector.
Typical Attack Vectors on BESS:
Remote Access Exploits – attacks through remote access. Most BESS systems have remote diagnostics and control functionality. Weak passwords, unsecured ports, lack of multi-factor authentication – all of these open doors for attackers. This is the simplest and most commonly exploited vector.
Man-in-the-Middle – attacks based on intercepting communications. If communication between EMS and BMS is not encrypted (and industrial protocols like Modbus don’t offer encryption by default), an attacker can intercept data and inject their own commands.
False Data Injection – injecting false data. An attacker substitutes readings from BMS sensors – for example, temperature data. The system “thinks” the batteries are cold, so it allows aggressive charging. In reality, the batteries are overheating, which can lead to thermal runaway – uncontrolled temperature rise and fire.
Denial of Service (DoS) – attacks blocking system operation. Overloading the communication network prevents the EMS from controlling the installation. At a critical moment, the storage facility doesn’t respond to grid operator commands – which can result in penalties for breach of Capacity Market contracts.
Firmware Manipulation – software manipulation. If firmware updates are not digitally signed and verified, an attacker can replace the software with malicious code. Importantly – this doesn’t have to happen over the network. Physical access to a service port during installation or maintenance is sufficient. This is why supply chain verification and service procedures are just as important as network security.
Attack Scenario and Its Consequences
To understand why BESS cybersecurity is not theory but real business risk, let’s consider a specific attack scenario:
Phase 1: Reconnaissance and Infiltration
The attacker identifies the energy storage facility through publicly available information – regulatory registers, grid connection announcements, employee LinkedIn profiles. They scan the operator’s IP ranges looking for open ports. They find a SCADA web interface with the manufacturer’s default password or exploit a vulnerability in outdated software (Remote Access Exploit). Alternatively, they send phishing to an O&M operator employee and obtain VPN credentials – lack of multi-factor authentication means the password alone is enough to take control.
Phase 2: Taking Control
After gaining access to the OT network, the attacker maps the system architecture. They use unencrypted Modbus communication (Man-in-the-Middle) to identify BMS, PCS, and EMS. They install a backdoor ensuring persistent access – this could be modified firmware in one of the controllers (Firmware Manipulation), which survives even a system restart. For weeks, they observe normal system operation, learning work patterns and waiting for the right moment.
Phase 3: The Attack Proper
Depending on the attacker’s motivation, scenarios can vary:
Sabotage Scenario (False Data Injection): The attacker manipulates temperature readings from BMS sensors – the system receives false data indicating low cell temperature. The BMS allows aggressive charging at high C-rate. In reality, the batteries are overheating. Exceeding critical temperature leads to thermal runaway – a lithium-ion battery fire that is extremely difficult to extinguish and can spread to neighboring containers.
Grid Destabilization Scenario (Denial of Service): At a moment of critical energy demand (winter peak, heatwave), the attacker overloads the communication network of dozens of energy storage facilities in the region. EMS systems cannot communicate with BMS and PCS – the storage facilities “freeze.” Sudden loss of balancing power in the system leads to cascading outages and regional blackout.
Ransomware Scenario: The attacker encrypts control systems and demands ransom. The storage facility is down, not generating revenue, and every day of downtime means financial losses and contractual penalties for not delivering contracted energy. Even after paying the ransom (which experts don’t recommend), there’s no guarantee of regaining control.
Market Manipulation Scenario: The attacker modifies optimization algorithms in the EMS – the storage facility buys energy expensive and sells cheap, the opposite of what it should do. Financial losses accumulate over weeks before anyone notices the anomaly in reports. By then, the attacker may be profiting from opposing positions in the energy market.
Consequences for Investors:
The effects of a successful attack extend far beyond direct losses:
Financial: Loss of revenue during downtime, contractual penalties for non-performance (PPA, Capacity Market), repair and system rebuild costs, increased insurance premiums, and in case of fire – potentially total loss of assets.
Legal: Liability for damage to the electrical grid, administrative penalties under national NIS2 implementation (up to EUR 10 million or 2% of turnover), personal liability of management (up to 300% of salary in some jurisdictions), potential civil claims from affected energy consumers.
Reputational: Loss of trust from investors and financing institutions, difficulties in obtaining financing for future projects, negative PR in an industry still building credibility.
This is Not Science Fiction:
Attacks on energy infrastructure are a reality. In 2015, an attack on the Ukrainian power grid (BlackEnergy) caused a blackout for 230,000 consumers. In 2021, a ransomware attack on Colonial Pipeline halted fuel supplies on the US East Coast for several days. In 2022, the Industroyer2 malware targeting Ukrainian electrical substations was discovered.
Energy storage systems, as a new and rapidly growing category of critical infrastructure, are natural targets – often deployed quickly, with pressure to minimize costs, without mature security procedures. Many installations use components from different manufacturers, complicating update management and increasing the attack surface.
Key Requirements and Deadlines
NIS2 has been transposed into national law across EU Member States. Key deadlines for covered entities typically include:
| Deadline | Obligation |
|---|---|
| 6 months | Self-identification and registration with national authorities |
| 12 months | Implementation of Information Security Management System (ISMS) and risk management measures |
| 24 months | End of transitional period – penalties can be imposed |
Financial Penalties as defined in Article 34 of NIS2:
- Essential entities: up to EUR 10 million or 2% of global turnover (whichever is higher)
- Important entities: up to EUR 7 million or 1.4% of global turnover
- Many national implementations also include personal liability for management

Practical Guide: What to Require and How to Verify
As a BESS investor, you must require security policies and certifications from all parties involved in your project. Below is a complete list of stakeholders and requirements.
- BESS System Supplier (BMS, PCS, battery containers)
What to require:
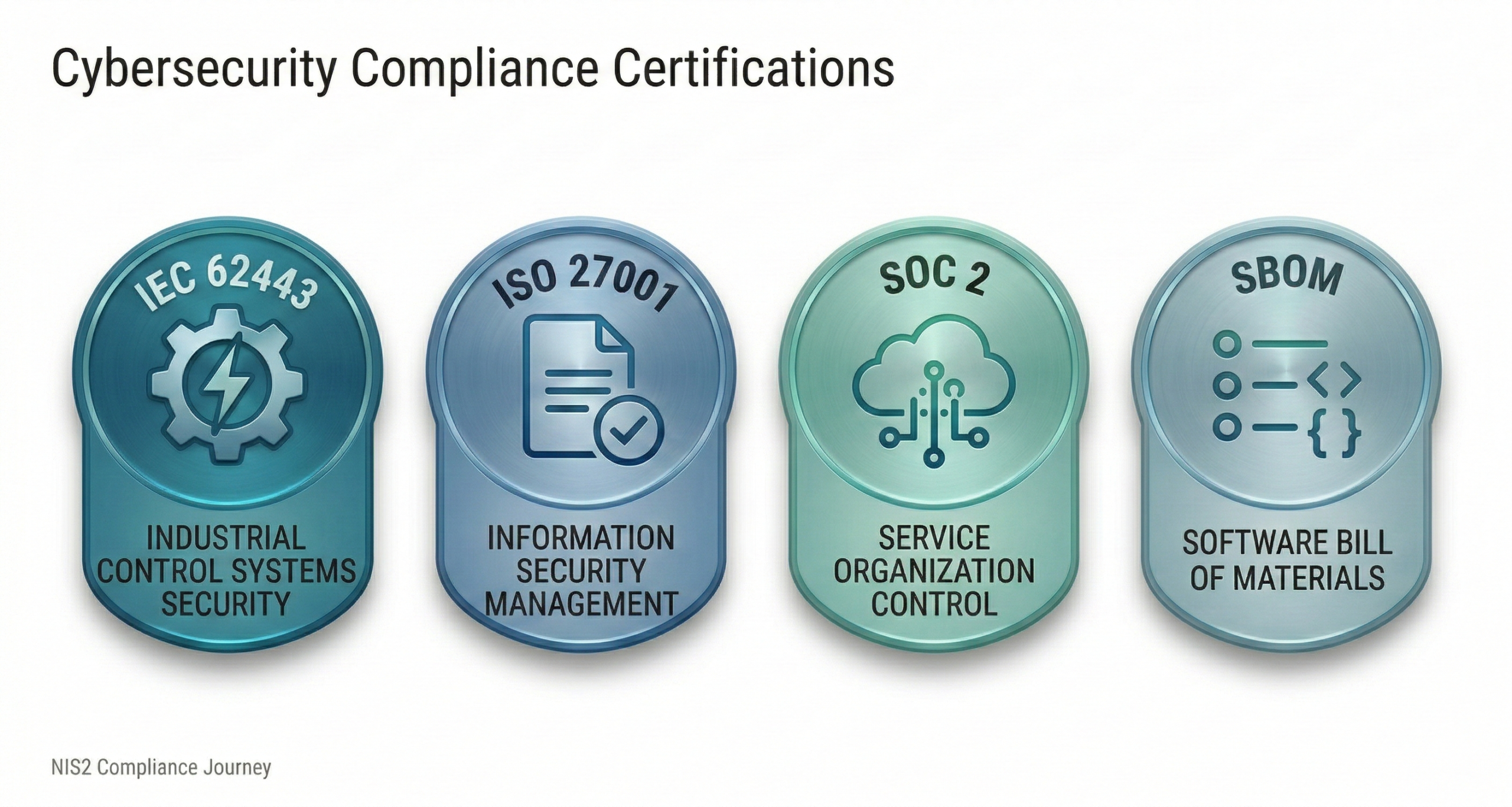
- IEC 62443-4-1 certificate (secure product development process) – the fundamental standard for industrial automation component manufacturers
- IEC 62443-4-2 certificate (functional requirements for components)
- SBOM (Software Bill of Materials) – list of all software components
- System security architecture documentation
- Vulnerability management policy and update schedule
- Declaration of server locations (does data leave the EU?)
Red flags:
- Default passwords that cannot be changed
- No support for TLS 1.2+ encryption
- Cloud platform outside EU without clear data transfer rules
- Inability to provide SBOM
- System Integrator / SCADA and EMS Provider
These are the key suppliers from a cybersecurity perspective – SCADA and EMS are the “brain” of the installation and the main attack targets.
What to require:
- IEC 62443-3-3 certificate (system requirements) – confirms the integrator deploys systems according to security standards
- ISO 27001 certificate for the integrator’s organization or equivalent security policy
- Documented secure configuration and deployment procedures
- Post-commissioning cybersecurity test report – this is the crucial document!
The cybersecurity test report should include:
According to IEC 62443-4-1 standard (section 9 / SVV), the report should cover:
- Security requirements testing (SVV-1) – verification of security functions (authentication, access control, encryption)
- Vulnerability testing (SVV-3) – scan for known vulnerabilities in system components
- Penetration testing (SVV-4) – simulated attacks on the system to identify weaknesses
- Network segmentation test – verification of isolation between zones (OT/IT)
- Configuration audit – review of security settings for all components
Important: According to IEC 62443-4-1, tests should be performed by an independent party – not by the same integrator who deployed the system. The standard defines three levels of independence: independent person, independent department, independent organization. For critical systems (like BESS), the highest level is recommended – an independent external organization.
- EPC Contractor
What to require:
- Information security policy in force within the organization
- Procedures for secure transfer of project documentation
- Access control to construction site and systems during execution
- Procedures for verifying subcontractors for security
- Commitment to transfer complete security documentation at handover (passwords, certificates, configurations)
- O&M Operator
What to require:
- Information security policy in the organization, ISO 27001 or equivalent document
- Remote system access management policy
- Security update installation procedures
- SLA for response in case of security incident
- Incident reporting procedures (compliant with NIS2 24h/72h requirements)
- Personnel cybersecurity training
- Asset Manager
The Asset Manager has access to operational and financial project data – this is sensitive information.
What to require:
- Information security policy in the organization
- Procedures for secure data storage and transfer
- Access control to reporting systems
- Identity verification procedures in communications (especially for financial instructions)
- Confidentiality and security clauses in the contract
- Optimizer / Aggregator
The optimizer has direct access to storage control – this is a critical attack vector.
What to require:
- ISO 27001 certificate or equivalent
- SOC 2 Type II certificate (if using a cloud platform)
- Platform security architecture documentation
- API communication encryption (TLS 1.2+)
- Authentication procedures (require MFA)
- Incident management policy
- Declaration of server and data processing locations
Cybersecurity Testing at Installation Commissioning
Before final acceptance of the BESS installation, we recommend conducting comprehensive cybersecurity tests. There is no single mandatory standard, but each of the following tests significantly reduces risk.
Recommended Tests:
- Penetration Testing
Simulated attack on the system to identify vulnerabilities that could be exploited by an attacker. Tests should include:
- Attempts to gain unauthorized access
- Industrial protocol testing (Modbus, IEC 61850)
- Privilege escalation attempts
- Remote access interface testing
- Vulnerability Assessment
Automated scanning of systems looking for known vulnerabilities (CVE). Identifies outdated software, missing patches, weak configurations.
- Configuration Audit
Review of security settings for all components:
- Have default passwords been changed?
- Is communication encryption enabled?
- Is the firewall configured correctly?
- Are logs enabled and stored?
- Network Segmentation Test
Verification that OT (control) networks are properly isolated from IT networks and the internet. Checking whether compromise of one segment allows passage to others.
- Incident Response Procedure Test
Simulation of a security incident to verify:
- Does the system detect anomalies?
- Do alerts reach the right people?
- Are response procedures clear and functioning?
Who Should Perform the Tests?
Tests should be performed by an independent audit firm specializing in industrial system security (OT/ICS). Such firms have experience testing SCADA systems without causing operational disruptions, which is crucial for energy infrastructure.
Look for firms with:
- Experience in the energy sector
- Knowledge of IEC 62443 and NIST SP 800-82 standards
- Certifications such as CREST, OSCP, GICSP (Global Industrial Cyber Security Professional)
- References from similar projects
Deliverable: Upon completion of testing, you should receive a detailed report containing: discovered vulnerabilities with criticality assessment, evidence (screenshots, logs), prioritized remediation recommendations, and attestation of testing conducted for compliance purposes.
Contractual Clauses – What to Include in Contracts
NIS2 requirements should be reflected in contracts with all suppliers. Key clauses include:
Product/Service Security Requirements:
- Minimum security level according to IEC 62443 (Security Level)
- Communication encryption obligation (TLS 1.2+)
- Multi-factor authentication (MFA) requirement
- Prohibition on default/shared passwords
Vulnerability Management:
- Obligation to report discovered vulnerabilities (within 24-48h)
- SLA for security patch delivery (critical: 48h, high: 7 days)
- Minimum product support period (10+ years for BESS)
- Update procedure without warranty loss
Incident Response:
- Obligation for immediate notification of security breach
- Cooperation in incident handling
- Evidence (log) retention for specified time
Audit and Verification:
- Right to conduct security audit at supplier
- Obligation for periodic penetration testing
- Compliance reporting on request
Flow-Down Clauses:
- Obligation to flow down security requirements to subcontractors
- Right to verify subcontractors
Practical Checklist for Investors
Before Signing Contracts (Development Phase):
- Include cybersecurity requirements in RfP specification
- Require IEC 62443, ISO 27001 or equivalent certificates as qualification criteria
- Define required contractual clauses (flow-down, audit, incidents)
- Budget for independent security audit at commissioning
Before Acceptance (Construction Phase):
- Verify security documentation from SCADA/EMS integrator
- Receive cybersecurity test report from integrator
- Commission independent audit/penetration testing from external firm
- Verify that all default passwords have been changed
- Ensure security documentation is complete
After Commissioning (Operational Phase):
- Implement update management procedures
- Establish security monitoring and incident response procedures
- Conduct periodic security reviews (minimum once per year)
- Train personnel on cybersecurity principles
- Maintain supplier register with risk assessment (NIS2 requirement)
How Can GreenEdge Solutions Help?
As a company specializing in technical advisory for BESS projects, we understand energy storage specifics and European regulatory requirements. In the area of cybersecurity, we offer:
🔍 Security Requirements Preparation for RfP
- Development of technical specifications incorporating NIS2 and IEC 62443
- Definition of supplier qualification criteria
- Preparation of contractual clause templates
📊 Supplier Documentation Verification
- Assessment of bidders’ certificates and security policies
- Analysis of proposed solutions’ security architecture
- Red flag identification and recommendations
📋 External Audit Coordination
- Assistance in selecting an independent audit firm
- Defining test scope
- Verification of reports and remediation recommendations
Contact us – we’ll help secure your BESS project against cybersecurity risks and ensure NIS2 compliance.
Summary
The NIS2 Directive is changing the rules of the game for all energy market participants. Key takeaways for BESS investors:
- Every grid-connected energy storage system will encounter NIS2 requirements – either as a directly regulated entity or indirectly through supply chain requirements
- Require certificates and security policies from all parties – BESS supplier, SCADA/EMS integrator, EPC contractor, O&M operator, Asset Manager, and Optimizer
- The SCADA/EMS integrator is the key supplier – require IEC 62443 certification and post-commissioning cybersecurity test report
- Commission independent testing – an external audit firm provides objective assessment and meets NIS2 requirements for supplier verification
- Include requirements in contracts – flow-down clauses, audit rights, incident procedures
- Time is working against you – 12 months to implement measures is less than you think, especially for new projects
Sources
- NIS2 Directive (EU 2022/2555) – full text: https://eur-lex.europa.eu/legal-content/EN/TXT/?uri=CELEX%3A32022L2555
- DLA Piper – NIS2 Supply Chain Security: https://www.dlapiper.com/en-us/insights/publications/2025/12/nis2-directive-explained-part-3-supply-chain-security
- 3rdRisk – NIS2 Questions to Ask Suppliers: https://www.3rdrisk.com/blog/seven-nis2-questions-to-ask
- CyberTrust365 – Supply Chain Security NIS2: https://www.cybertrust365.com/en/supply-chain-security-nis2/
- TÜV NORD – IEC 62443 Certification: https://www.tuv-nord.com/en/services/cybersecurity/iec-62443/
- CertX – IEC 62443 Penetration Tests: https://certx.com/cybersecurity/how-to-implement-cyber-security-acc-to-iec-62443-ep-4-penetrations-tests/
- Cyberintelsys – ICS/SCADA Penetration Testing: https://cyberintelsys.com/ics-scada-penetration-testing/
- ISMS.online – NIS2 Contract Requirements: https://www.isms.online/nis-2/supply-chain/contracts/requirements/
- ENISA – NIS2 Guidance: https://www.enisa.europa.eu/topics/nis-directive
Listen to the Podcast
Learn more about cybersecurity requirements for BESS projects: Episode 11 – NIS2 and Cybersecurity in BESS Projects
Related articles:
BESS + PV: Why Hybrid Projects are the Future of Poland’s Renewable Energy Market
Anatomy of a BESS Container: What Are You Really Buying for Millions of Euro?
Battery Energy Storage for Manufacturing: When Does BESS Make Sense for Industrial Facilities?